See the assignment's PDF available on BrightSpace for task descriptions and submission requirements.
Level 10
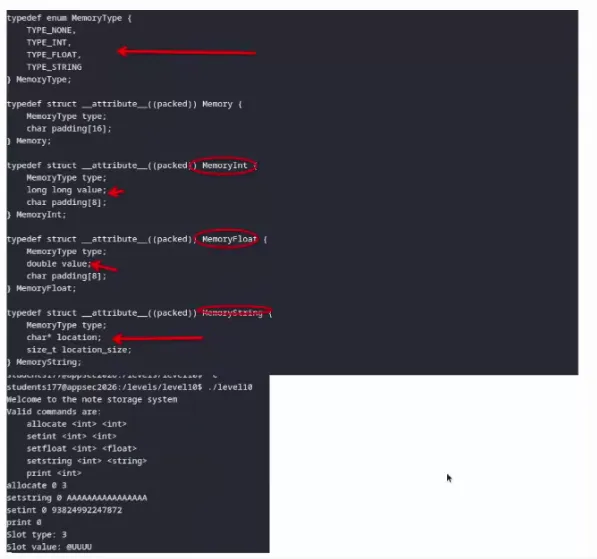
1) This program manages memory slots using structs; each slot is 20 bytes. Bytes 0–3 hold the type tag, bytes 4–11 hold the value (int) or pointer (string). The structs share the same layout, so an operation meant for one type silently works on another.
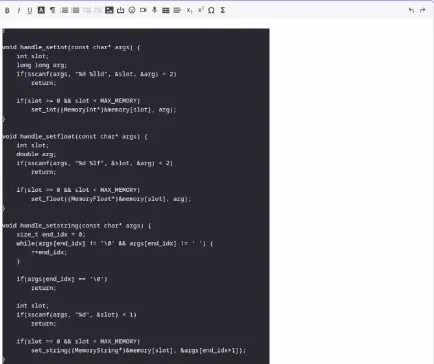
Looking at handle_setint:
void handle_setint(const char* args) {
int slot;
long long arg;
if(sscanf(args, "%d %lld", &slot, &arg) < 2)
return;
if(slot >= 0 && slot < MAX_MEMORY)
set_int((MemoryInt*)&memory[slot], arg); // no type check!
}
It writes to bytes 4–11 without checking the slot's current type. If the slot is a
string, those bytes are the pointer field. Calling
setint 0 <address> overwrites the pointer with an arbitrary integer.
The type tag stays TYPE_STRING, the size stays whatever it was.
Then print 0 triggers:
fwrite(str->location, 1, str->location_size, stdout);
It reads location_size bytes from our arbitrary address — leaking memory from
anywhere in the process. Classic type confusion.